System sometimes shut down abnormally.
Important files are deleted and altered.
Antivurus are disabled.
If you have the above problems, your PC may have been infected by an Trojan horse Exploit.Win32.CVE-2010-2568.gen which may have great danger to your computer.
Where is Exploit.Win32.CVE-2010-2568.gen from?
Baleful websites, malicious links, or corrupted websites.
Strange email or junk email.
Dangerous pop-up messages.
Free software or programs that attached with Trojan horse.

Some symptoms of Exploit.Win32.CVE-2010-2568.gen.
It infiltrates into users’ machine secretly.
It will decelerate the performance of your computer and highly take up your system space.
It will threaten your system safety and pilfer your vital information.
It make your protecting tool lose some of its functions so as to bypass its detections and removal.
Available approaches about removing Exploit.Win32.CVE-2010-2568.gen
Approach one: get rid of Exploit.Win32.CVE-2010-2568.gen manually
Approach two: remove Exploit.Win32.CVE-2010-2568.gen automatically
Detail guides about the two removal methods
Approach one: get rid of Exploit.Win32.CVE-2010-2568.gen manually
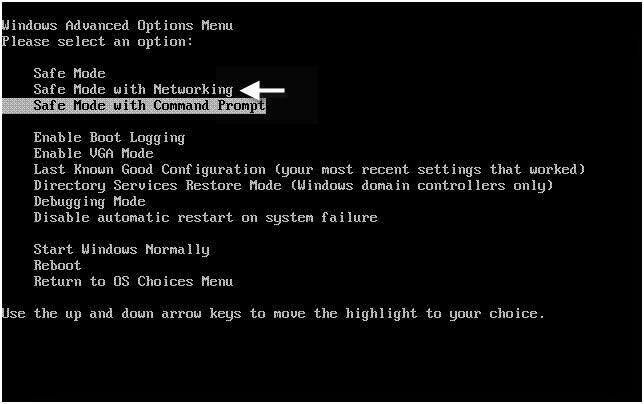
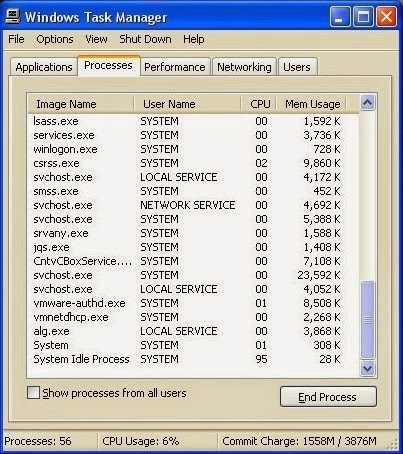
Step 2: Press Ctrl+Alt+Del keys together and stop Exploit.Win32.CVE-2010-2568.gen
processes in the Windows Task Manager.
Step 3: Open Control Panel from Start menu and search for Folder Options. When Folder Options window opens, click on its View tab, tick Show hidden files and folders and non-tick Hide protected operating system files (Recommended) and then press OK.

%AppData%\<random>.exe
%CommonAppData%\<random>.exe
C:\Windows\Temp\<random>.exe
%temp%\<random>.exe
C:\Program Files\<random>
Step 4: Search for all infected files and registry entries and remove them from your computer as follows:
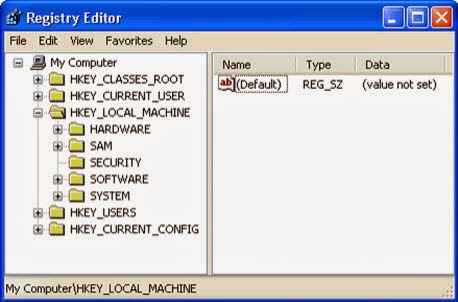
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "<random>" = "%AppData%\<random>.exe"
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run "<random>" = "%AppData%\<random>.exe"
Approach two: remove Exploit.Win32.CVE-2010-2568.gen automatically
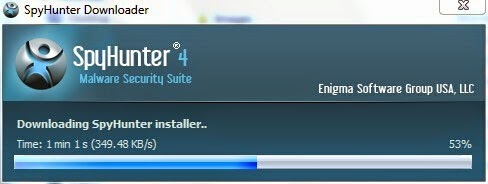
Step 1: Install SpyHunter
1) Download SpyHunter here or click the below button to download the file.
2) Double click on SpyHunter-Installer.exe to install the program.
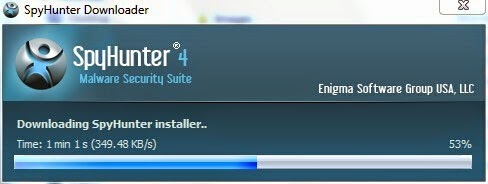
3) After the installation, click Finish.

Step Two: Fix all the detected threats with SpyHunter
1) Open SpyHunter and click Scan Computer Now to allow the program to start a scan on your computer.

2) SpyHunter will now start scanning your computer as shown below.

3) When the scan is completed, all the threats in your computer are successfully detected. Click Select All and then click Remove button to uninstall it.

Note: SpyHunter is a leagal and useful antivirus program that can give your PC real-time protection. You can download SpyHunter here and run a scan on your computer after its installation is complete.
2) Double click on SpyHunter-Installer.exe to install the program.
3) After the installation, click Finish.

Step Two: Fix all the detected threats with SpyHunter
1) Open SpyHunter and click Scan Computer Now to allow the program to start a scan on your computer.

2) SpyHunter will now start scanning your computer as shown below.

3) When the scan is completed, all the threats in your computer are successfully detected. Click Select All and then click Remove button to uninstall it.

Note: SpyHunter is a leagal and useful antivirus program that can give your PC real-time protection. You can download SpyHunter here and run a scan on your computer after its installation is complete.
If you want to speed up the performance of your computer, remove your privacy items produced by online searches, delete junk files and uninstall malware, you are advised to have a reliable optimizer such as TuneUp Utilities, Advanced SystemCare, RegCure Pro and 360 Amigo System Speedup. Here takes RegCure Pro as an example.
1) Download RegCure Pro here or click the below button to download the file.
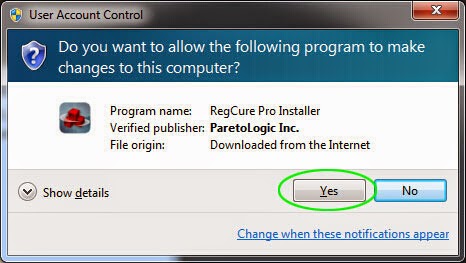
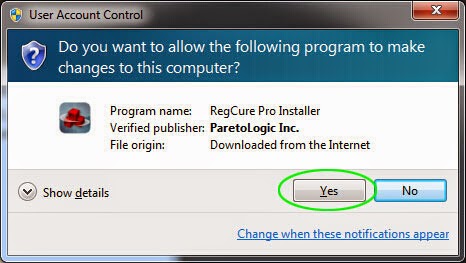
2) Run the RegCureProSetup Application and click the Yes button to install the program step by step.
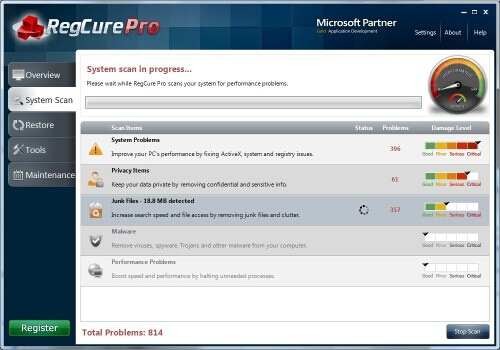
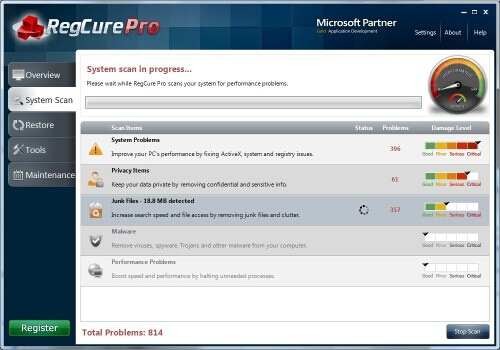
3) When the program is successfully installed, double click on its desktop shortcut to open it. On the Overview tab, check all the scan settings and then click on the Click to Start Scan button to run a system scan on your computer. The first system scan will take some time, please be patient.

The screenshot of the system scan progress is shown below.
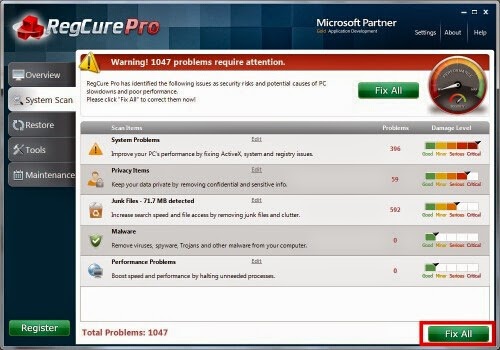
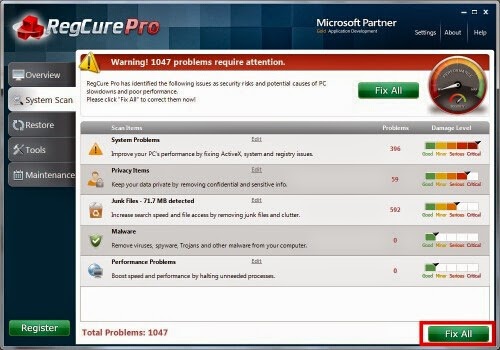
4) When the system scan is done, click on Fix All button to completely remove all the performance problems in your computer.
1) Download RegCure Pro here or click the below button to download the file.
2) Run the RegCureProSetup Application and click the Yes button to install the program step by step.
3) When the program is successfully installed, double click on its desktop shortcut to open it. On the Overview tab, check all the scan settings and then click on the Click to Start Scan button to run a system scan on your computer. The first system scan will take some time, please be patient.

The screenshot of the system scan progress is shown below.
4) When the system scan is done, click on Fix All button to completely remove all the performance problems in your computer.



No comments:
Post a Comment