There is some attacks occurring in Brazil and the "hackers" are using an ransomware software to crypt and change the file extensions, the file extensions are being changed to .Teslacrypt 3.0, the "hackers" are requesting bitcoins in order to send a password to unzip an .exe that will uncrypt the files.
A person have payed the bitcoin and he has shared the .exe that uncrypt the files, i will attach the files for someone that want try to make a reverse engineering on it to try to make a generic uncrypt for this kind of situation.
If your PC is infected by Teslacrypt 3.0 ransomware, your critical files will be encrypted and you are always displayed an alert saying that your files are encrypted, you have to pay money or bitcoin to get them back, if not, you will never use them again. Don't be frightened by it, although your PC is locked by it, you can get professional help from computer security experts. Teslacrypt 3.0 Ransomware is developed by cyber criminals to cheat innocent computer users' money. What you need to do is to get rid of Teslacrypt 3.0 Ransomware from your PC as early as possible to avoid further losses.
How to Remove / Uninstall Teslacrypt 3.0 Ransomware
Method one: manually remove Teslacrypt 3.0 Ransomware from the infected computer.
In case any mistake might occur and cause accidental damages during the virus removal, please spend some time in making a backup beforehand. Then follow these steps given as below.
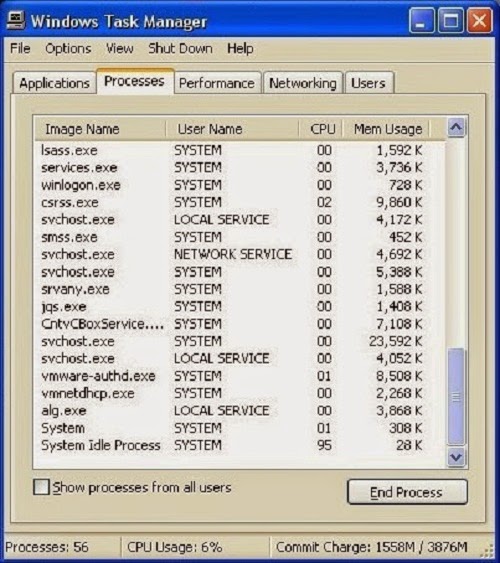
1. Press Ctrl+Alt+Del keys together and stop Teslacrypt 3.0 Ransomware
processes in the Windows Task Manager.
2. Find out the following files relative to Teslacrypt 3.0 Ransomware
and then delete them all.
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
%Temp%\random.exe
%AllUsersProfile%\Application Data\random
3. Search the following registry entries in your Registry Editor and then remove all of them.
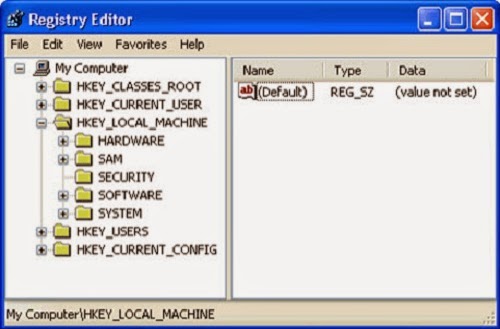
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "<random>" = "%AppData%\<random>.exe"
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run "<random>" = "%AppData%\<random>.exe"
4. Restart your computer and check the effect.
Step One: Install SpyHunter
1) Download SpyHunter here or click the below button to download the file.2) Double click on SpyHunter-Installer.exe to install the program.
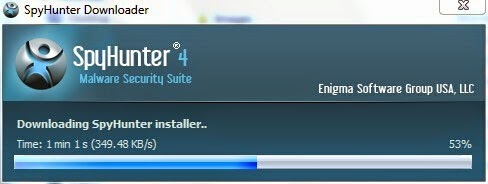
3) After the installation, click Finish.

Step Two: Fix all the detected threats with SpyHunter
1) Open SpyHunter and click Scan Computer Now to allow the program to start a scan on your computer.
2) SpyHunter will now start scanning your computer as shown below.

3) When the scan is completed, all the threats in your computer are successfully detected. Click Select All and then click Remove button to uninstall it.

Step Three: Optimize Your PC
If you want to speed up the performance of your computer, remove your privacy items produced by online searches, delete junk files and uninstall malware, you are advised to have a reliable optimizer such as TuneUp Utilities, Advanced SystemCare, RegCure Pro and 360Amigo System Speedup. Here takes RegCure Pro as an example.1) Download RegCure Pro here or click the below button to download the file.
2) Run the RegCureProSetup Application and click the Yes button to install the program step by step.
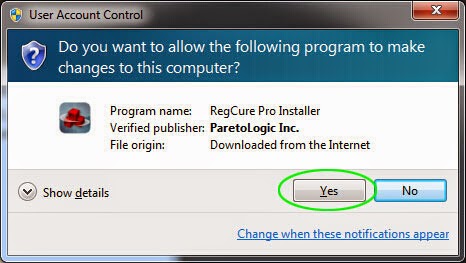
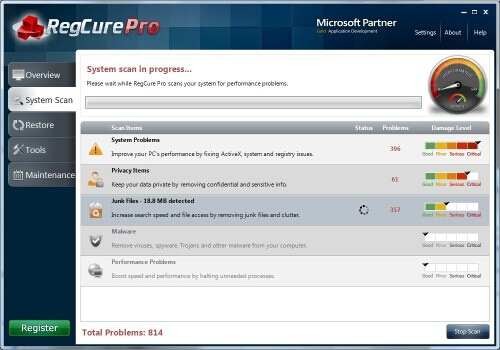
3) When the program is successfully installed, double click on its desktop shortcut to open it. On the Overview tab, check all the scan settings and then click on the Click to Start Scan button to run a system scan on your computer. The first system scan will take some time, please be patient.

The screenshot of the system scan progress is shown below.
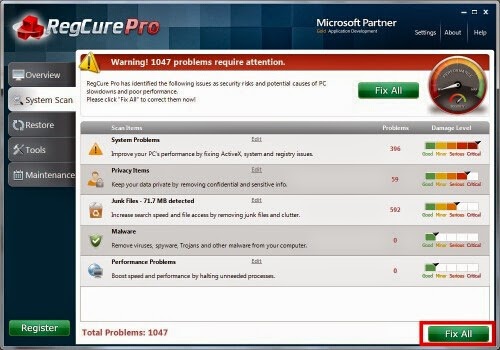
4) When the system scan is done, click on Fix All button to completely remove all the performance problems in your computer.
Reminder: SpyHunter is a legitimate and effective antivirus program that can give your PC real-time protection. You can download SpyHunter here and run a scan on your computer after its installation is complete. RegCurePro is professional in optimizing your system so that you can study,work or enjoy yourself on the computer without any interruption.



No comments:
Post a Comment